Business email compromise
Business email compromise refers to the act of cybercriminals gaining access to a business email account and masquerading as the account owner to help their fraudulent emails appear legitimate. One of the most common tactics is fraudulent wire transfers. Cybercriminals send emails to employees who can access a company’s funds and request transactions like wire transfers or ACHs. In other instances, a cybercriminal might contact a worker who has access to employee information, such as a payroll or human resources associate, hoping to gain personal data to perpetuate identity theft.
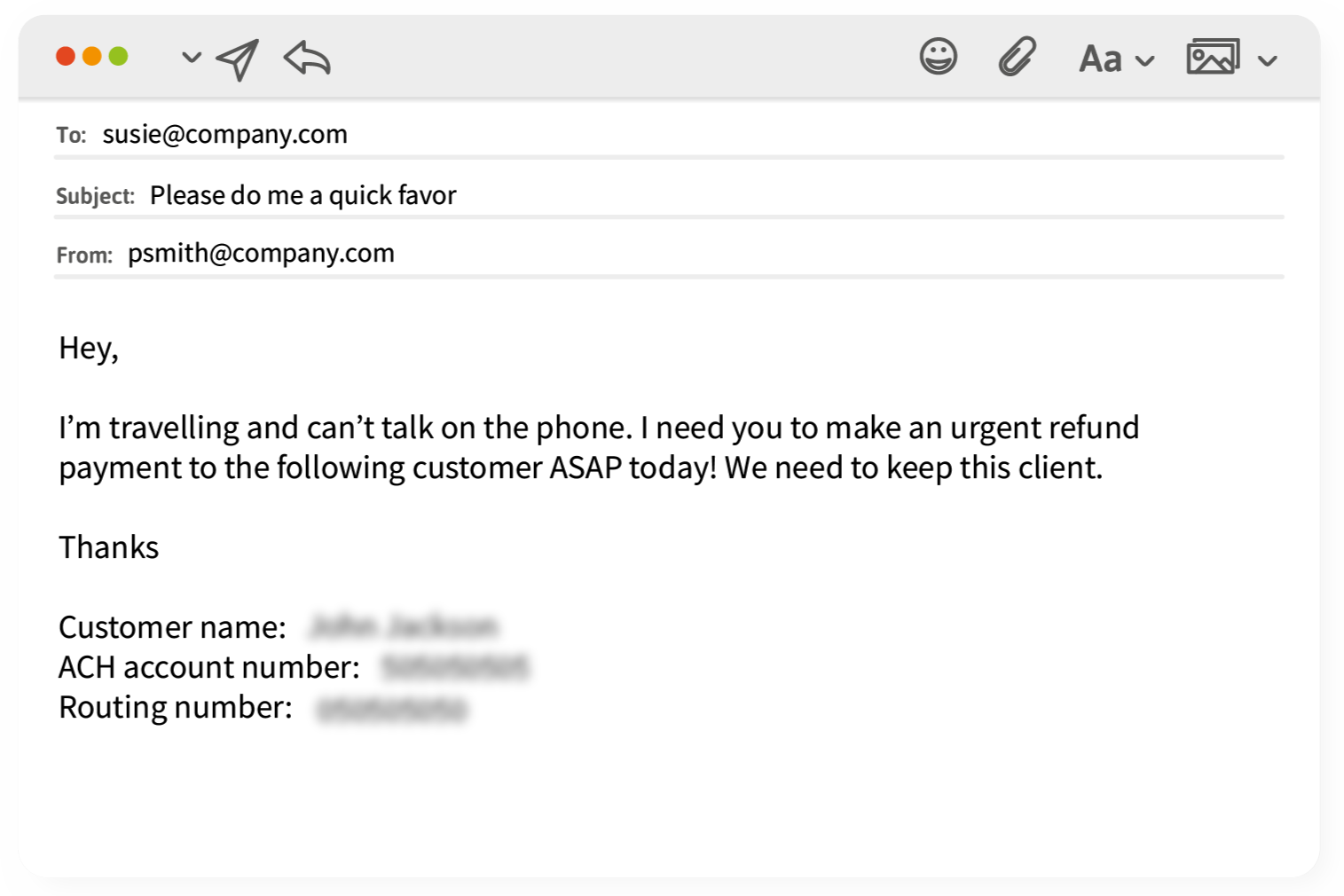
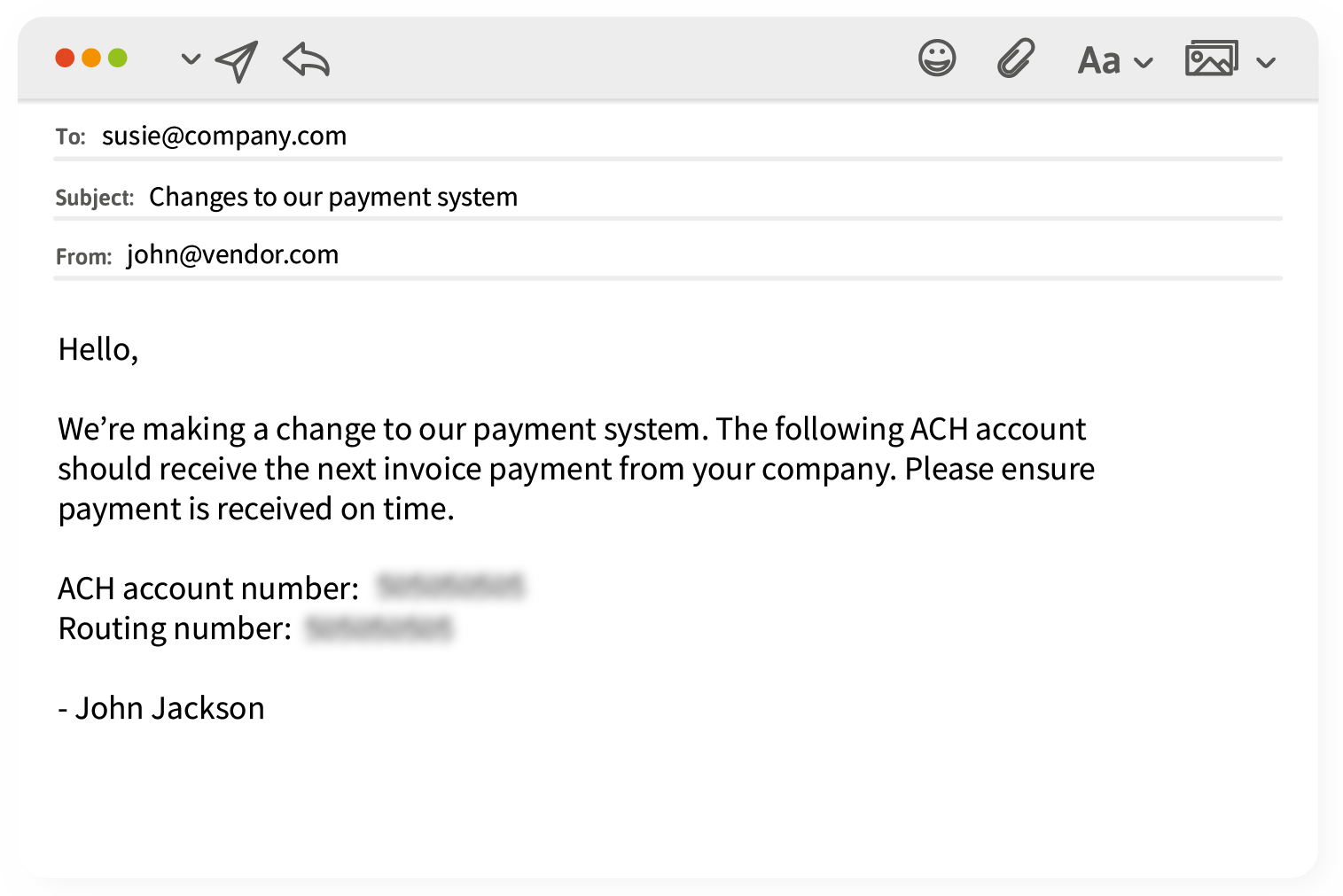
Here are two common examples:
![]()
1. The scammer emails you pretending to be a vendor asking that you send the next payment to a new ACH destination.
2. The scammers impersonate a company executive explaining that they are somehow occupied and can’t talk on the phone but have an urgent need for a payment or money transfer.